Search This Blog
Topics
About Us
Welcome to our research blog for our 4th year project at the School of Industrial Design at Carleton University.
Learn More
Learn More
From the Past
-
▼
2014
(74)
-
▼
October
(45)
- Blood bricks instead of Mud bricks
- Q/A With Virginia 10.17.2014
- Putting it All Together
- Our Insights
- Collaborative Insight
- Failed Project | Bill Gates' Toilet
- Projects | The Hippo Roller
- Water Demand in Longido
- MPower in Longido
- Water Sanitation in Longido and Tanzania
- Learning from Past Failures
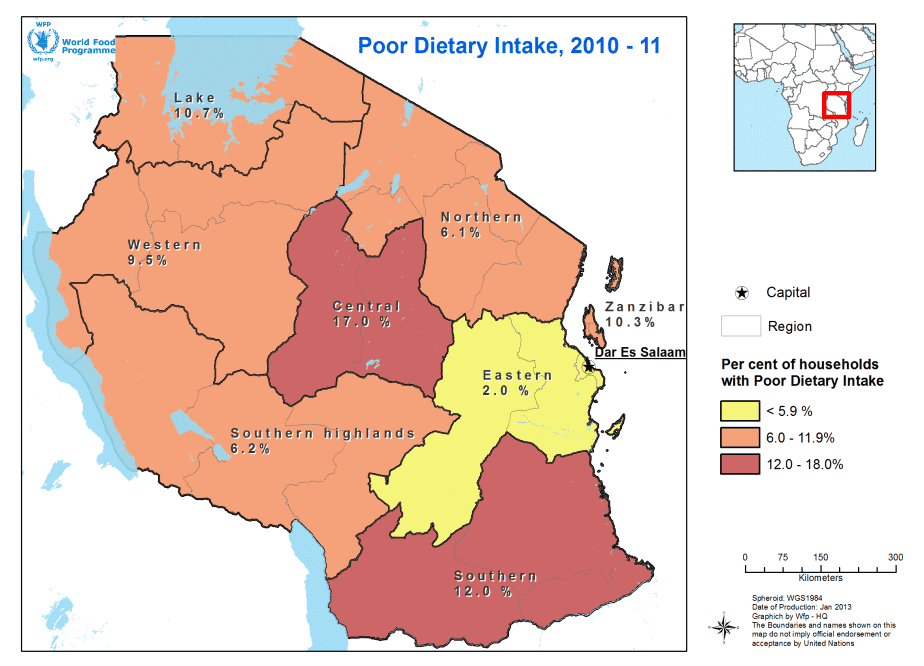
- Food Insecurity and Vulnerability
- Fortune at the Bottom of the Pyramid
- Addressing the [Water] Sustainability Crisis
- Sorting your trash: a responsible and worthy endeavor
- Water Harvesting in Lushoto, Tanzania
- Garbage site turns into bread basketin Tanzania
- Lighting in Rural Tanzania
- MondoChallenge charity work: Water programs & Inte...
- Volunteer Tourism in Tanzania: How it really is
- Sketch: Ideas about terrariums
- Telecommunication in Africa
- A summary of popular Tanzanian dishes
- Recreation in Longido
- Women in Longido and Micro-Business
- Looking back at our Assumptions
- Solutions Too Expensive?
- Q/A Conference call with Virginia Taylor - October...
- Project TEMBO
- Women of the Maasai Culture
- Maasai On the Move - A Documentary
- Cooking as a Source of Indoor Air Pollution
- Photos of Longido Community
- Maasai Pastoralists: Diversification & Poverty
- Afrigadget
- Cola Life - Utilizing Existing Distribution Systems
- Gravity Light
- Design for Need
- Bottles as building blocks: Agriculture
- Playing in Tanzania continued: Montessori Educatio...
- Maasai Voices on Climate Change
- Playing in Tanzania
- Biogas
- Living Walls - Maasai Tech
- Design for the Other 90%
-
▼
October
(45)